Privileged Access Management Policy Template
Privileged Access Management Policy Template - Clearly define roles and responsibilities for. One of the first steps to privileged access management (pam) success is defining clear and consistent policies that everyone who uses and. This policy outlines the requirements and responsibilities for individuals with privileged access to university information technology. They are based on compliance. Use this easily customizable sample policy as a starting point to build a privileged account management (pam) policy for your organization.
One of the first steps to privileged access management (pam) success is defining clear and consistent policies that everyone who uses and. Use this easily customizable sample policy as a starting point to build a privileged account management (pam) policy for your organization. Clearly define roles and responsibilities for. This policy outlines the requirements and responsibilities for individuals with privileged access to university information technology. They are based on compliance.
This policy outlines the requirements and responsibilities for individuals with privileged access to university information technology. They are based on compliance. Use this easily customizable sample policy as a starting point to build a privileged account management (pam) policy for your organization. One of the first steps to privileged access management (pam) success is defining clear and consistent policies that everyone who uses and. Clearly define roles and responsibilities for.
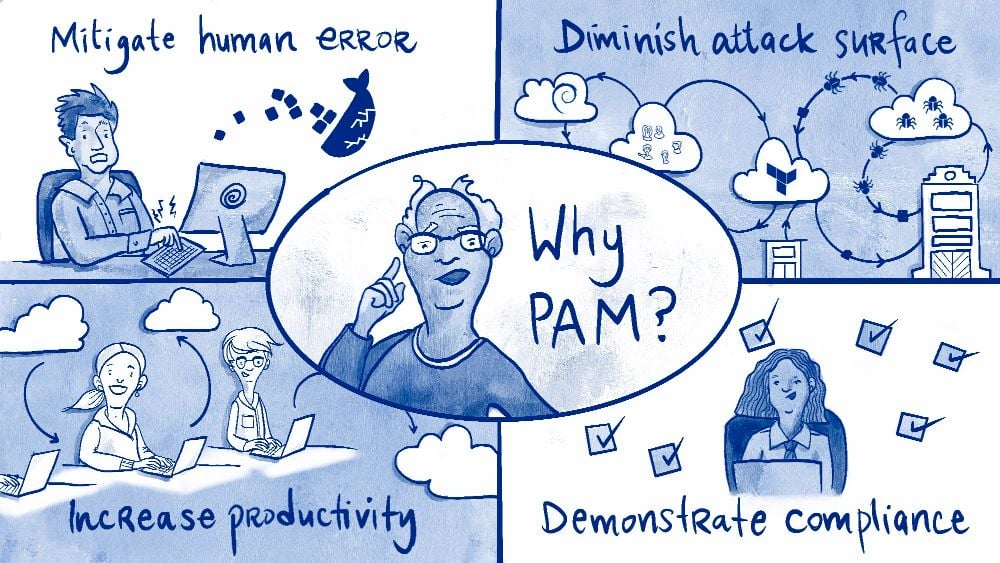
What is PAM Security? Privileged Access Management Explained StrongDM
This policy outlines the requirements and responsibilities for individuals with privileged access to university information technology. Clearly define roles and responsibilities for. One of the first steps to privileged access management (pam) success is defining clear and consistent policies that everyone who uses and. Use this easily customizable sample policy as a starting point to build a privileged account management.
Privileged Access Management (PAM) SecureISS
Use this easily customizable sample policy as a starting point to build a privileged account management (pam) policy for your organization. They are based on compliance. This policy outlines the requirements and responsibilities for individuals with privileged access to university information technology. Clearly define roles and responsibilities for. One of the first steps to privileged access management (pam) success is.
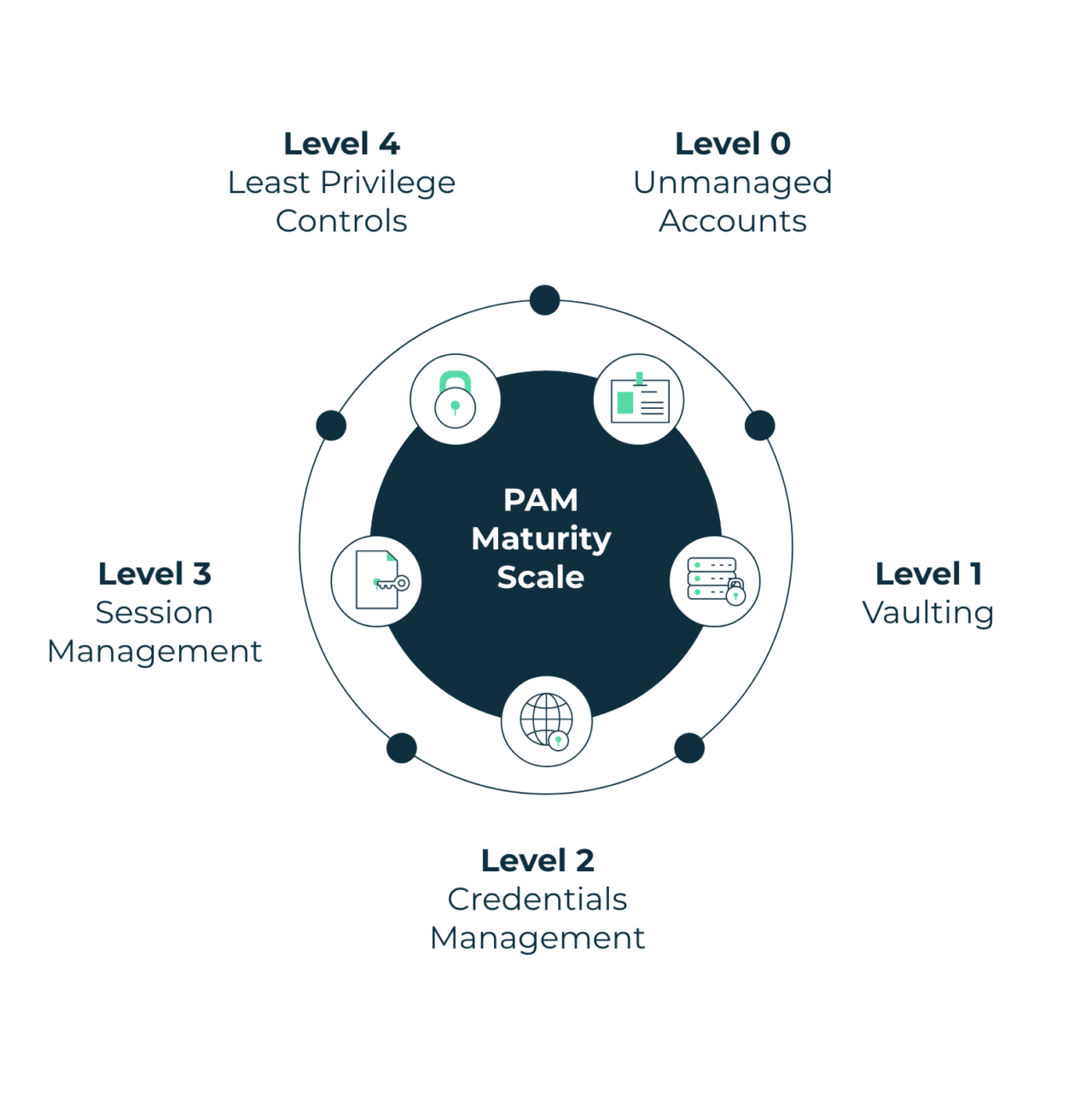
What is Privileged Access Management (PAM)? Delinea
They are based on compliance. This policy outlines the requirements and responsibilities for individuals with privileged access to university information technology. Use this easily customizable sample policy as a starting point to build a privileged account management (pam) policy for your organization. Clearly define roles and responsibilities for. One of the first steps to privileged access management (pam) success is.
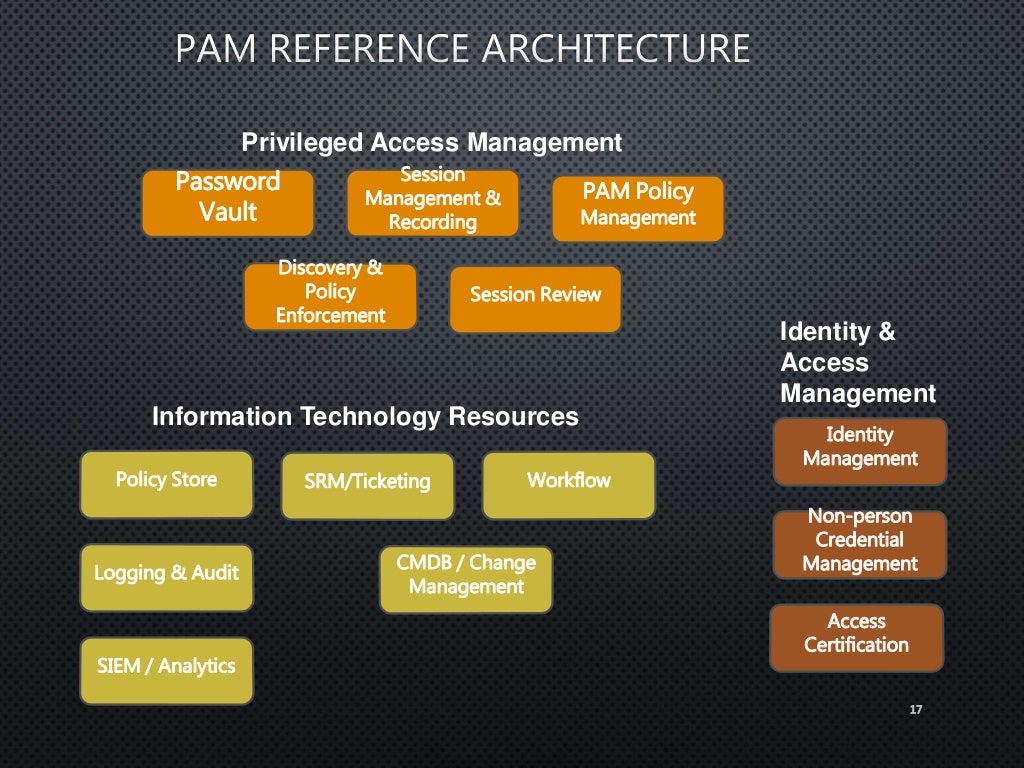
Privileged Access Management 2016
Use this easily customizable sample policy as a starting point to build a privileged account management (pam) policy for your organization. One of the first steps to privileged access management (pam) success is defining clear and consistent policies that everyone who uses and. Clearly define roles and responsibilities for. This policy outlines the requirements and responsibilities for individuals with privileged.
Advantages of Privileged Access Management Services for Compliance with
One of the first steps to privileged access management (pam) success is defining clear and consistent policies that everyone who uses and. They are based on compliance. Clearly define roles and responsibilities for. Use this easily customizable sample policy as a starting point to build a privileged account management (pam) policy for your organization. This policy outlines the requirements and.
Privileged Access Management Policy Template
Clearly define roles and responsibilities for. One of the first steps to privileged access management (pam) success is defining clear and consistent policies that everyone who uses and. This policy outlines the requirements and responsibilities for individuals with privileged access to university information technology. Use this easily customizable sample policy as a starting point to build a privileged account management.
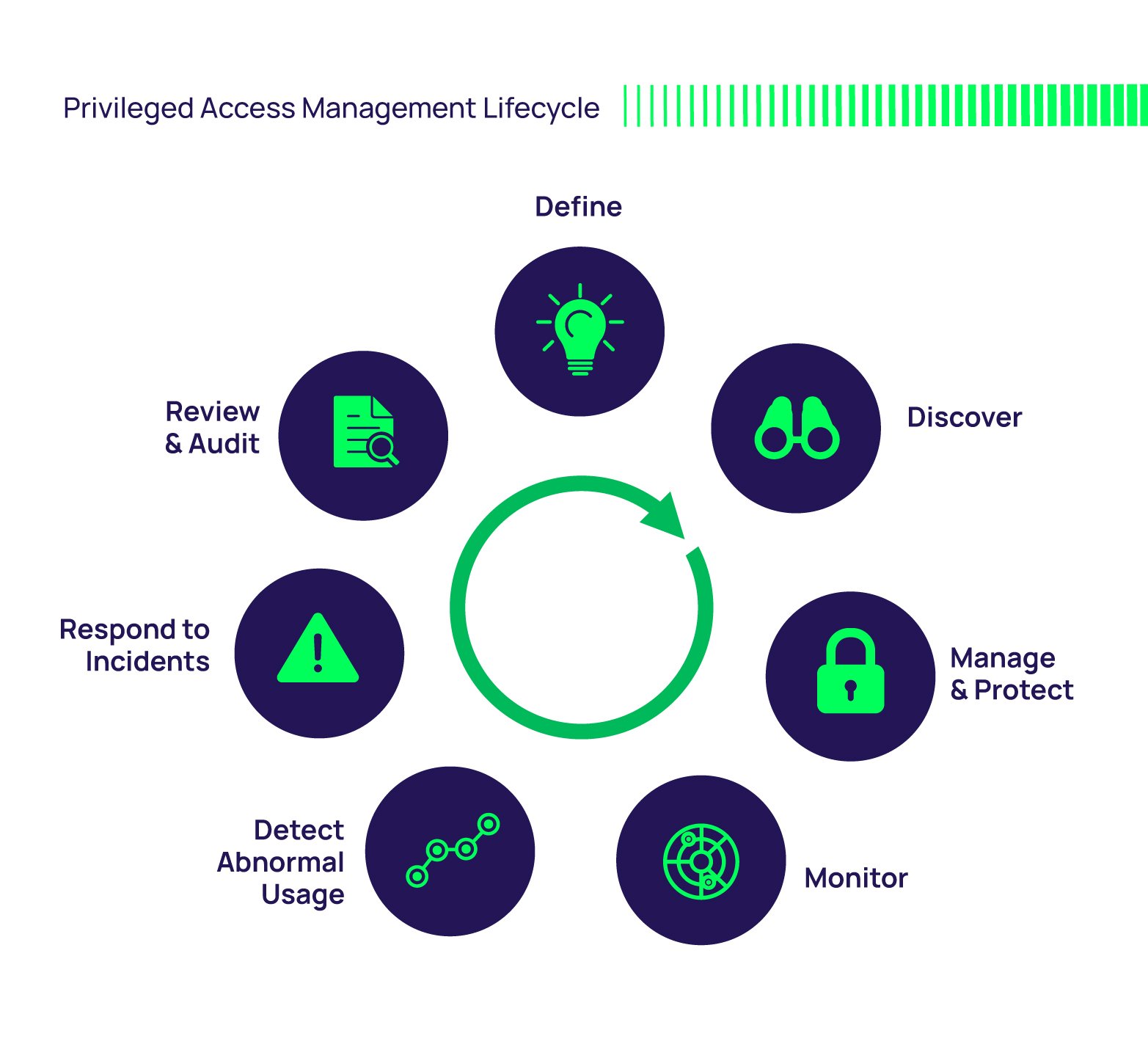
Essentials of Privileged Access Management Fortra
One of the first steps to privileged access management (pam) success is defining clear and consistent policies that everyone who uses and. This policy outlines the requirements and responsibilities for individuals with privileged access to university information technology. Clearly define roles and responsibilities for. They are based on compliance. Use this easily customizable sample policy as a starting point to.
Download Privileged Access Management Policy Template Whitepaper
One of the first steps to privileged access management (pam) success is defining clear and consistent policies that everyone who uses and. They are based on compliance. This policy outlines the requirements and responsibilities for individuals with privileged access to university information technology. Clearly define roles and responsibilities for. Use this easily customizable sample policy as a starting point to.
Privileged Access Management Policy Template
They are based on compliance. Clearly define roles and responsibilities for. This policy outlines the requirements and responsibilities for individuals with privileged access to university information technology. One of the first steps to privileged access management (pam) success is defining clear and consistent policies that everyone who uses and. Use this easily customizable sample policy as a starting point to.
What is Privileged Access Management? Security Priority 1
They are based on compliance. Use this easily customizable sample policy as a starting point to build a privileged account management (pam) policy for your organization. This policy outlines the requirements and responsibilities for individuals with privileged access to university information technology. Clearly define roles and responsibilities for. One of the first steps to privileged access management (pam) success is.
They Are Based On Compliance.
This policy outlines the requirements and responsibilities for individuals with privileged access to university information technology. One of the first steps to privileged access management (pam) success is defining clear and consistent policies that everyone who uses and. Clearly define roles and responsibilities for. Use this easily customizable sample policy as a starting point to build a privileged account management (pam) policy for your organization.